Smart cards and associated accessories are a fascinating combination of cutting-edge technology and wearables. By combining the best of both worlds, they are quickly becoming an invaluable asset for organisations worldwide.
Organisations must consider numerous factors when embracing this state-of-the-art technology, from smart cards to powerful electronic readers, printers, and even modern lanyards.
However, any decision to use smart cards must also consider where accessories fit in with existing processes to create a seamless experience and secure environment for customers and employees alike.
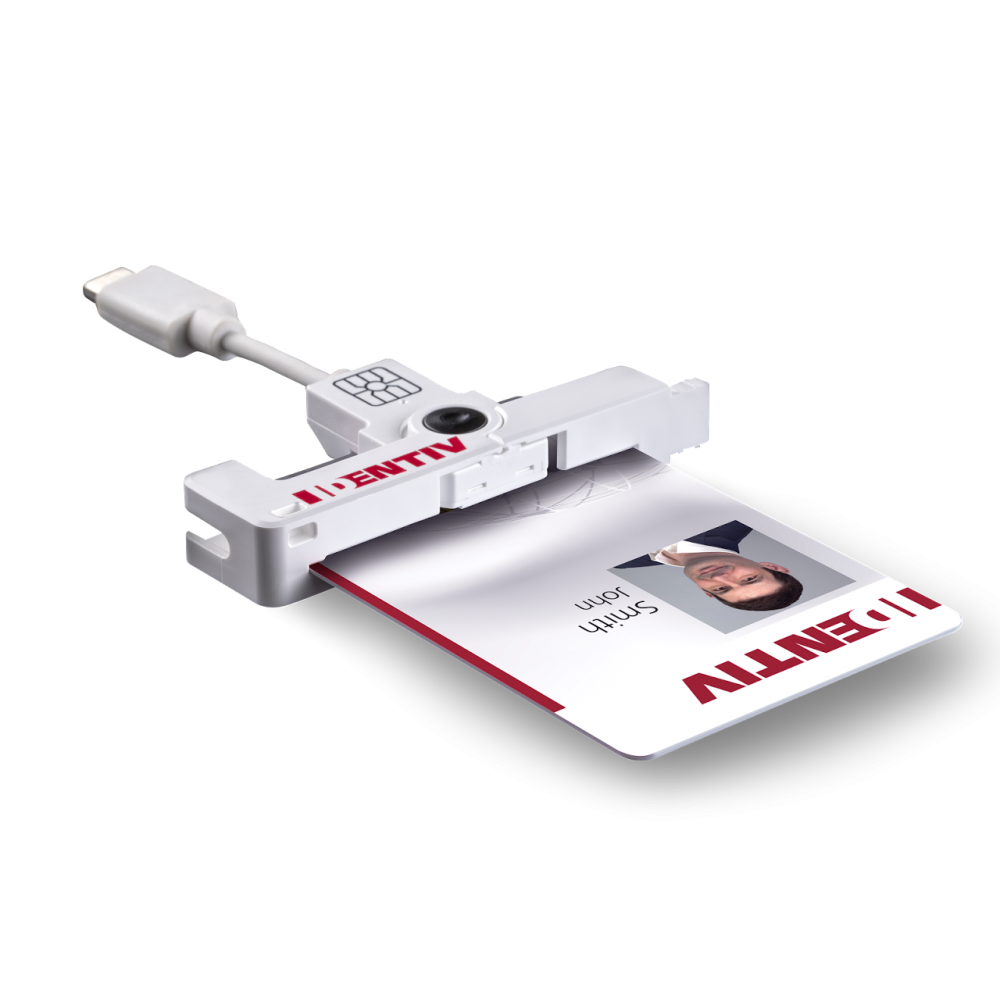
Smart cards are incredibly valuable tools, offering state-of-the-art security and risk management control to any enterprise network. Businesses must invest in the right accessories to make the most of these secure systems. These include smart card readers to access information, ID card printers to create IDs and ID holders for storing IDs securely.
When used together effectively, smart cards and their associated technologies and accessories form an integral part of a secure IT infrastructure. The combination of a reputable brand smart card and suitable accessories can help reduce losses from fraudulent use, increase the reliability of access control solutions, and ensure optimal data security for your business.
Related Reading: Where Are Smart Cards Used?
The Importance of Simplicity
Smart cards and their accessories offer a unique combination of convenience and security, but their usefulness ultimately depends on how easily users adopt the technology. Smart cards can be invaluable assets if implemented efficiently, creating an effective bridge between convenience and security that encourages customers to use them.
However, suppose their use involves too many steps or is too difficult to understand. In that case, users won’t have the motivation to utilise the technology and businesses won’t reap the benefits of using smart cards. Therefore, smart card implementation must prioritise simplicity to make them useful for all users.
For any new technology to be adopted quickly and efficiently, you must put a clear set of guidelines in place with an accessible onboarding process. Smart card technology is no exception. Adoption should be designed with novice and experienced users in mind so that everyone can take advantage of what this innovative technology offers.
Companies should prioritise making the onboarding process for smart cards straightforward, user-friendly, and quick to get customers up and running as soon as possible while offering comprehensive support for the smart card's advanced capabilities. This will guarantee that all users can benefit from the convenience and security associated with smart cards.
Types of Smart Cards and Accessories
When integrating these cards into an organisation’s business model, it’s essential to consider the available types and their unique features and capabilities. Once you determine which types of smart cards best suit your needs, it's easy to begin unlocking their many benefits. More organisations are discovering how useful they can be in simplifying everyday tasks while increasing safety measures across the board.
Related Reading: What Are The Different Types Of Smart Cards?
Factors That Impact the Ease of Use and Adoption
Smart card technology has the potential to revolutionise how people make payments, access services, and process data. While it is a great technology, its adoption heavily depends on several factors that affect its ease of use.
Smart cards and accessories must have a well-designed user interface to make the experience seamless and pleasant. Additionally, smart card implementation must be compatible with existing systems and infrastructure to maximise convenience.
Smart card technology can significantly benefit users, but these factors must be considered when assessing its ease of use and adoption. And it’s not just the technology side of things either. You must consider smart card accessories such as lanyards, ID card holders, and ID badge clips.
Related Reading: 5 easy steps to choosing an ID card printer
Best Practices for Promoting Ease of Use and Adoption
When introducing smart cards, user feedback and testing can be instrumental in allowing companies to identify how their users react to the new technology before implementing it on a wide scale.
By anticipating potential problems that may arise from introducing a new system, businesses can ensure the smooth adoption of this advanced technology, achieving the desired outcomes with minimal disruption. Businesses should not underestimate the value of involving the smart card users in the process. When done right, this can help foster a sense of connection between user experience and product design.
Smart cards are becoming increasingly popular in security and identification thanks to their reliability and modern convenience. While there are many uses for smart cards, including access control and in sectors like health care, their implementation requires direct user support and access to technical assistance for anyone involved.
Users can ensure the process works smoothly by providing clear and concise instructions on utilising smart cards correctly. Investing in high-quality card readers and accessories is also a must for any successful smart card application. These devices act as a bridge between the system hardware and the cardholder's credentials.
Smart card implementations are complex and require a high level of expertise and resources. That's why it is essential to partner with a specialist provider with the background, resources, and experience to ensure everything goes according to plan.
A key piece of the puzzle is reliable smart card accessories like smart card readers and printers built for the task. Having a trusted vendor ready to provide technical support when necessary will enhance the chances of successful implementation. Working with experienced professionals who have access to top-quality smart cards and accessories can make all the difference in achieving a successful smart card deployment.
Related Reading: How Can I Reduce Cybersecurity Threats with Smart Cards?
Security Considerations for Smart Card Adoption
Smart cards are revolutionising the way we approach online security and identity protection. These cards offer an unmatchable level of protection, and are also incredibly useful for various transactions, extending far beyond everyday purchases to cover banking institutions, healthcare services, and government applications.
Such comprehensive security in a single card makes them an ideal solution for businesses seeking to keep their data safe from potential threats and fortify access to their resources. The right implementation promises convenience and reliability simultaneously, ensuring that users can transact confidently and with peace of mind.
When it comes to smart card security, you must take measures to ensure the safety and integrity of personal data. These measures are essential to good security practices, from encrypting data on smart cards to implementing multi-layered identification methods such as PINs or biometric authentication.
You should regularly update protocols and software to remain up-to-date with the latest threats and regulations. Perhaps most importantly, only those with the right level of authority should have access to certified smart card printers and accessories. By following these steps, users can rest assured that their sensitive information is guarded against potential risks.
Related Reading: Can Smart Cards Be Cloned?
Future Developments in Smart Cards and their Accessories
Several exciting developments and trends in smart cards and accessories are worth considering. These include:
Contactless smart cards, such as the NXP MIFARE® smart card range, are becoming increasingly popular for everyday transactions. These cards are incredibly convenient since users simply have to tap their cards against a card reader to complete the transaction or gain access to the workplace.
Biometric authentication offers an additional layer of protection that revolutionises the way we think about and manage security. Integration of biometric authentication, such as fingerprints and facial recognition, can provide access control, identify individuals quickly and securely, verify transactions and guarantee compliance with specific regulations. With biometrics, there's no need to remember passwords or answer personal questions.
The marriage of smart cards and accessories with the internet of things (IoT) opens up immense potential for connectivity. Smart cards and accessories can now communicate with various electronic devices, gadgets, systems, and machines. With the card owner’s consent, these devices can send and receive data directly from their intelligent companions. This data can help automate a wide range of tasks like controlling access to premises or exchanging payments for goods purchased online.
Smart cards and accessories offer an efficient way for businesses worldwide to manage payments, security, and a wide variety of other resources. As these technologies are becoming more accessible and affordable in emerging markets, there's a growing potential for increased adoption by smaller businesses struggling with archaic methods.
Plan for Smart Card Success
Smart cards and accessories have become increasingly prevalent in various industries and offer various advantages. With this increased adoption, it is essential to consider ease of use when implementing smart card solutions.
Smart card accessories are designed to simplify processes, increase safety and security, and streamline operations. However, the result can be confusion and inconvenience without a proper understanding of how they work.
By taking the time to understand customer needs, assess user experience feedback, and test applications before launch, one will benefit from improved usability, faster adoption of smart card technologies and greater user satisfaction.
Smart cards and their accompanying accessories provide unparalleled advantages in the modern workplace. Smart card implementations enable quick and secure authentication, providing user convenience while enhancing an organisation’s security posture.
Smart card solutions are also priced competitively, making them both affordable and accessible. Smart card technology is a compelling choice that offers organisations improved efficiency and cost savings.
Contact Universal Smart Cards Today
Are you looking to invest in smart cards for your business or event?
If security and ease of adoption are critical to your business, then have a chat with USC, and we’ll be able to advise you appropriately. Get in touch today to discuss your requirements or concerns and get answers to any questions you have.
You can also contact us by phoning 0333 700 0078 or emailing [email protected] for further information.